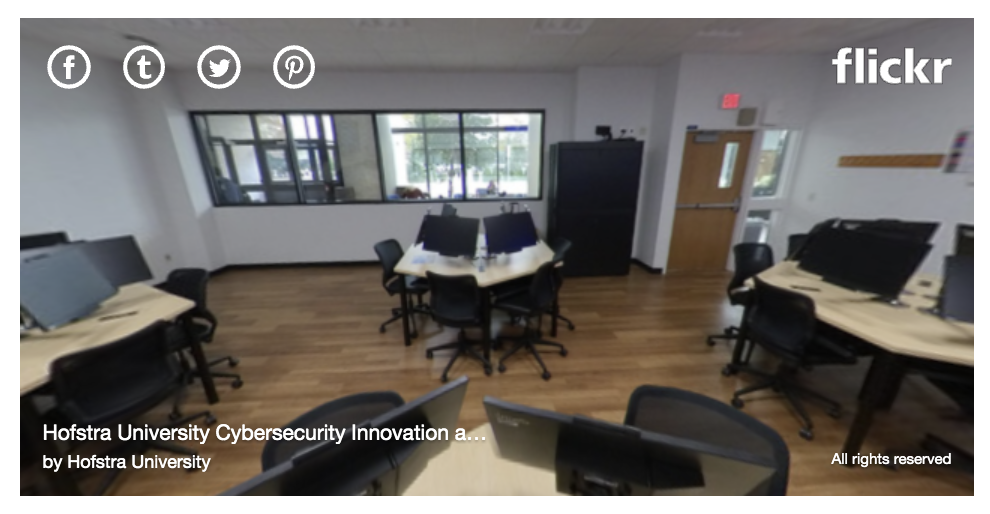
The Cybersecurity Innovation and Research Center is a specialized facility for training the next generation of cybersecurity professionals that is shared between the Department of Computer Science and the Department of Information Systems and Business Analytics (ISBAN). The Center consists of the Cyber Lab (aka. Cybersecurity War Room) and a mini server room. The lab features 36 Tiny-in-One (TIO) workstations, 5 large wall-mount displays, Cisco networking hardware, servers, and IoT devices. The lab is supported by a mini server room that houses the lab’s infrastructure with an isolated network and dedicated internet connection. The lab is designed to provide an immersive environment through its cyber range and VMware environments. The cyber range allows faculty to build scenarios that students can engage in for hands-on lab exercises. The lab systems are equipped with software like: Cellebrite UFED Touch2 (software used by law enforcement, military, and intelligence agencies to protect, extract and maintain the integrity of data on a mobile device), CryptTool2 (e-learning cryptology software that detects items that are not strictly malicious but pose some sort of risk to the user), Metasploit Pro (professional penetration testing software, made available to Hofstra students through Hofstra University’s partnership with Rapid7).
The Center ...
- Provides innovative, hands-on educational opportunities using sophisticated technology and simulation software to create hyperrealistic cyberattack scenarios.
- Collaborates with industry, government, and other academic institutions to promote cybersecurity research projects with multiple applications.
- Is a training and educational resource for the New York metropolitan region by providing workshops for K-12 students through working professionals which create a pipeline to fill the growing demand for a well-educated cybersecurity workforce across all industries.
The Center is a joint project of the Fred DeMatteis School of Engineering and Applied Science and the Frank G. Zarb School of Business.
Facilities
The Center is equipped with cutting-edge technology and simulation software to create hyperrealistic cyberattack scenarios. It features 36 computers, a separate server room, and status boards on the walls that students use to manage the operations of a cybersecurity exhibition or share ideas and information.
It is one of the only academic ‘war room’ facilities in the New York metropolitan area with a cyber range, an immersive, virtual experience that replicates the high-pressure environment of an attack and allows students to work through it in real time, from detection and response to repair and recovery.

Center Events
Hack-a-thon/Capture the Flag: Hosted annually by the New York City/Long Island IC2 Chapter
Hofstra CTF Competition: Hosted annually by the Zarb School of Business
AI Takes Center Stage at the Technology in Business Schools Roundtable
Cybersecurity In Action: Crisis Simulation and Response
Get academic program information ...
UNDERGRADUATE | GRADUATE
Other Offerings
- Hofstra WiCyS Club
- Sample Student Projects: Michael Raymond
- Course List:
Faculty

Dr. Gurvirender Tejay

Dr. Hak J. Kim
Co-Director
Associate Professor of Information Systems and Business Analytics
Chair of the Department of Information Systems and Business Analytics
Contact us
Location: Room 108 C.V. Starr Hall
Co-Director
Hak Kim, PhD
Room 331 Business School Building
516-463-4529
hak.j.kim@hofstra.edu
Co-Director
Xiang Fu, PhD
Room 103 Adams Hall
516-463-4787
xiang.fu@hofstra.edu